Potential Threats To NFT Discords
Malicious OAuth Phishing Links
Discord Security Alerts
Since the newest Discord phishing attack is a little hard to understand, I've made an image showing a valid oauth request on the left, and the scam oauth on the right. ALWAYS check where you're being redirected to. Please share for awareness.
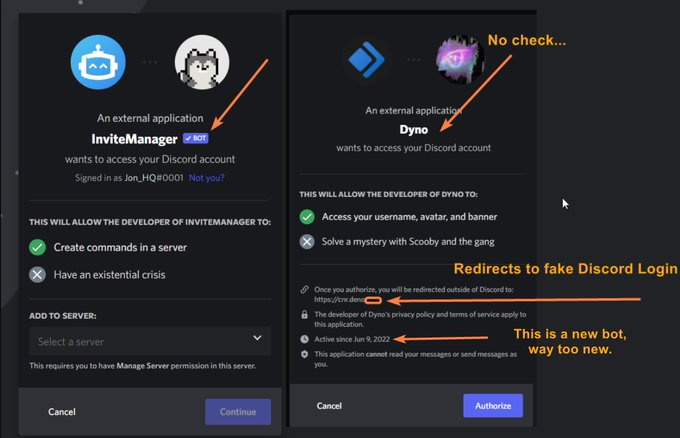
ALWAYS be super careful about entering your Discord login information anywhere. Check the URL. Cut the domain out and manually type in "http://Discord.com" when you get sent to a login page This scam oauth request MIGHT BE LINKED BY A REAL BOT. But it will go to the fake.
I've added a question about this new scam on my Discord security quiz, and I'm proud to announce 1000 people have taken this quiz already! If you haven't taken the quiz, please do so below, it goes over most of the phishing schemes out in the wild: https://t.co/AwBzFkX9eT
Project and Blue Check Twitter Impersonation
Twitter accounts are no longer safe and attackers are going after them too now. I'll try and push out some general tips around handling Twitter accounts securely.

Fake Verification Bots and Scanning QR Codes
This Discord is using a VERIFIED bot renamed. It is a fake Wick bot, requiring you to verify. It asks you to scan a QR code to verify - this logs you in on a new client the attackers control. The attackers are leveling up again, stay safe folks. This one is nasty. https://twitter.com/NotoriousPDUBBB/status/1510857058224316417
Discord Phishing Schemes
Were you aware that the average NFT Discord has over 12 users with Mod or Team level perms? An series of infographics:
If they get this string of text from any moderator or team member, your NFT Discord is compromised.

Here are the FIVE ways they'll get to that Discord token and phish you:

They'll try to get you to drag any 'bookmark' to your bookmark bar, usually for 'verification' NEVER DO THIS.
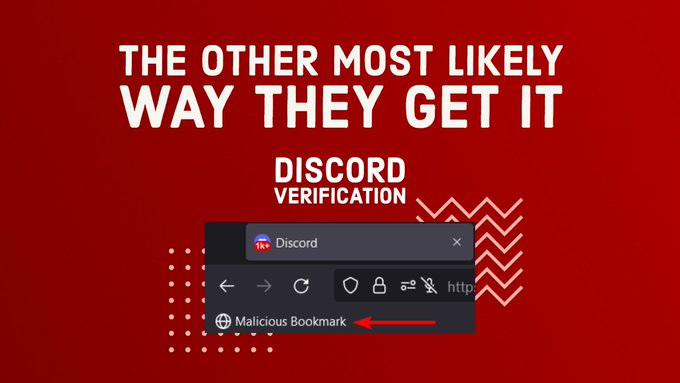
If a project asks for a bookmark to get whitelisted, NEVER DO IT.

You can expose your Discord token through even a casual screenshare, NEVER DO IT.

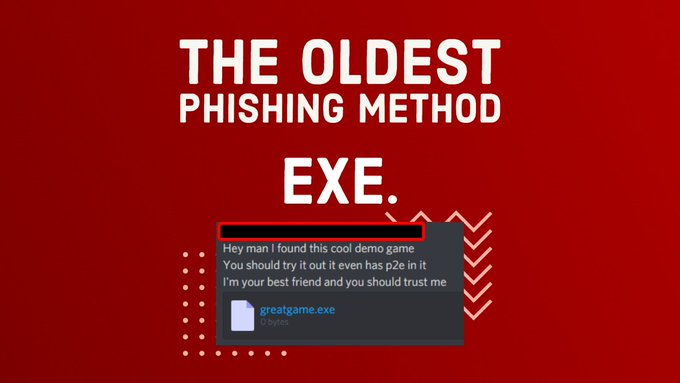
And finally, the least likely route, but where this all started - never download and execute any files or code (including JS) that you don't review.
These attacks have developed over the last couple months. There are new attacks every day...

Huge shoutout to @TisarNFT for help on this ! If anyone else needs help on infographics reach out to her - We only get through this wild west of phishing by working together and sharing information, especially in easy to digest ways. Please share this thread to your team!
Impersonation Attacks
Discord Security Tip
I've been thinking a lot about impersonation attacks the last few days. It is common for phishers to pose as a team member to try to scam normal users. Let's dig into it a little. h/t to @crystalgroves for alerting me to this impersonator:
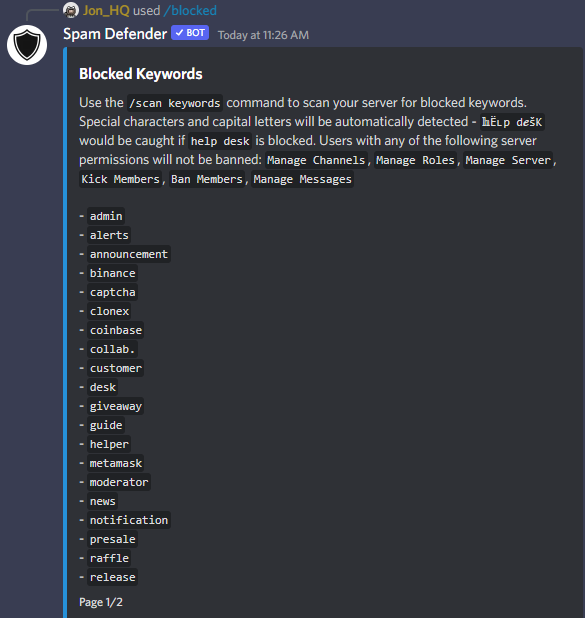
First of all, if you want to block phishers from impersonating your team, get https://spamdefender.io or https://hashbot.gg Both will scan your server for new joins or nickname changes, automatically detect non-standard characters, and ban those trying to impersonate you.
I also highly recommend every member of your Discord staff add a suffix to their nickname in the server, this could be as simple as "| Mod" or "| Team". This makes it harder for impersonators to slightly misspell your name, i.e. someone made a "Jor_HQ" account once.
Lastly, Man in the Middle impersonation attacks - this is partially what used to occur a lot when phishers were doing screenshare scams to snag Discord tokens. Essentially you impersonate multiple people in order to send 'true' information to your victim.
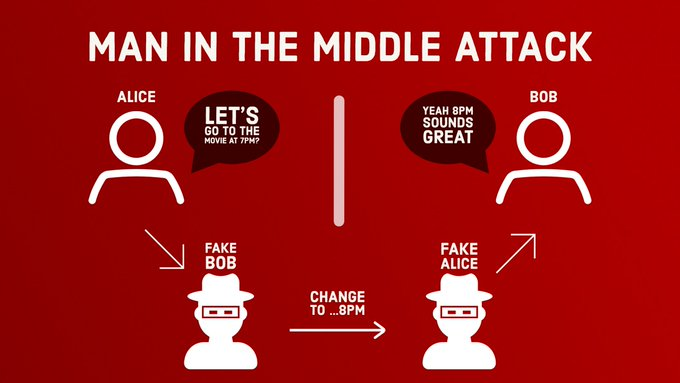
So - something I am being a 𝗹𝗼𝘁 more careful about how I interact with individuals requesting audits of servers. Simply asking them to repeat something you send to them over Twitter is not enough in my opinion. So how do we verify people on Discord from Twitter dms?
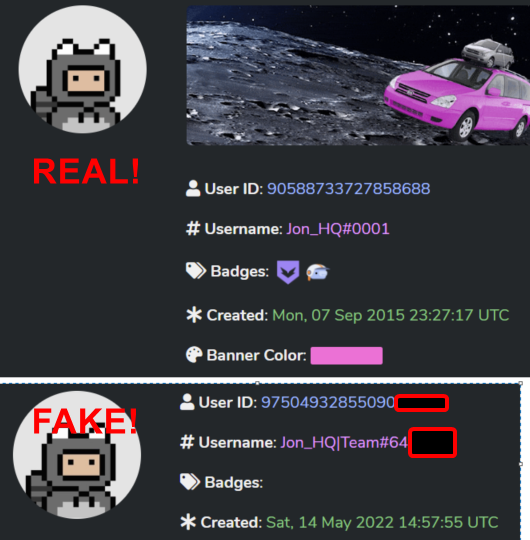
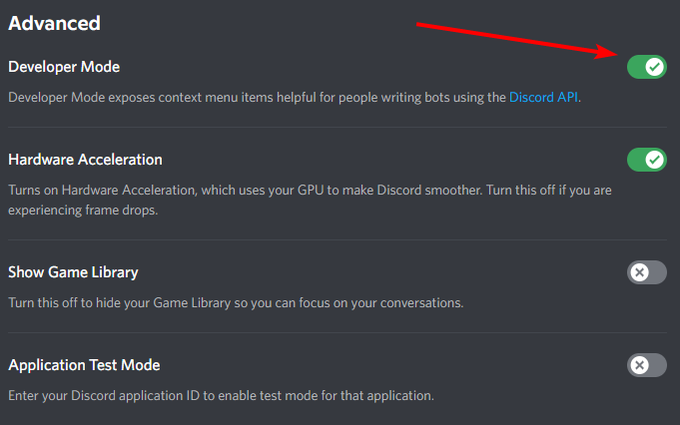
#1: Discord IDs - these you cannot fake. To be able to see these, go to Settings -> Advanced and toggle this option below. Now right click on anyone's username, you can verify a Discord ID. My ID is 90588733727858688 - unless a message comes from that account it is not me.
#2: Connected accounts I haven't seen a case yet where attackers have compromised official Twitter accounts to create phishing Discord accounts. So check the connections on the profile you're talking to. While not foolproof this gives you some peace of mind.
#3: Mutual connections While not the safest route, being introduced to someone by someone you already know and trust can help lessen that you're talking to an imposter. Do not rely on listed 'mutual followers' or 'mutual friends' to verify their identity though, only intros.
What we have learned: Impersonation will happen. More projects and individuals should publish their server ID and Discord user ID on Twitter/Website/Opensea to help folks verify them. A wide swath of interconnected official accounts is harder to impersonate. Stay safe frens.
Rumors of Mod/Admin Bribes
Discord Security Alert
As if moderators and admins getting phished weren't enough. I now have multiple independent confirmations that attackers are straight up bribing any of your Discord staff with up to $100k... What can you as a project owner do?
1: You can't afford to pay your mods $100k. Limit the damage moderators can do. They shouldn't have permissions to announce things. There should be an anti-nuke bot watching their actions Remove mod trust from the equation. If you can't do this properly hire someone who can.
2: Get to know your team. Literally, like get to 𝗸𝗻𝗼𝘄 them. Teams might not need to be doxxed publicly, but internally every team member with Discord perms should be very doxxed. (Also usually a legal requirement anyways) The only counter to a massive bribe is a reputation.
3: Use cold admins, please for the love of god use cold admins. If you take the bribe, you just say you got phished. This excuse doesn't work if you implement the Cold Admin Protocol. It is too hard to phish a cold admin, and anyone claiming so is sus.
4: Bot devs aren't safe anymore either This extends into the recent compromises around Mee6/Ticket Tool/GiveawayBoat. It is impossible for you to vet these external bots' full dev and support teams. Limit what bots you use, and host bots in house where you can securely.
5: Review everything The whole goal here is to reduce attack vectors - but the internal compromise vector is something not discussed very often. So sit down and think about your team and try to identify potential issues. Limit access where you can, and verify people's identity.
I was already planning on talking about this today, but seeing @9tales_NFT's huge tweet thread about tracking down one of these scammers inspired me to tweet about this even more. Stay safe out there folks..
Voice Impersonation of Founders
Discord Security Tip
When a phishing method stops working as well, scammers don't stop. They evolve. There have been rumors of attackers now impersonating project founders and replicating how their voice sounds using voice modulators. How should teams react?
First of all, why this is a potentially debilitating attack. Project founders or lead team members will be on Twitter spaces, a lot. This makes it extremely easy to get a voice sample of well, anyone. Voice/voiceprint should never ever be used to verify someone.
NFT teams need to set up a secure secondary line of communication to verify dangerous requests. I recommend Slack. You can force team members to use 2FA and Slack works well for a private group chat setting. While your community might demand Discord, your team can use Slack.
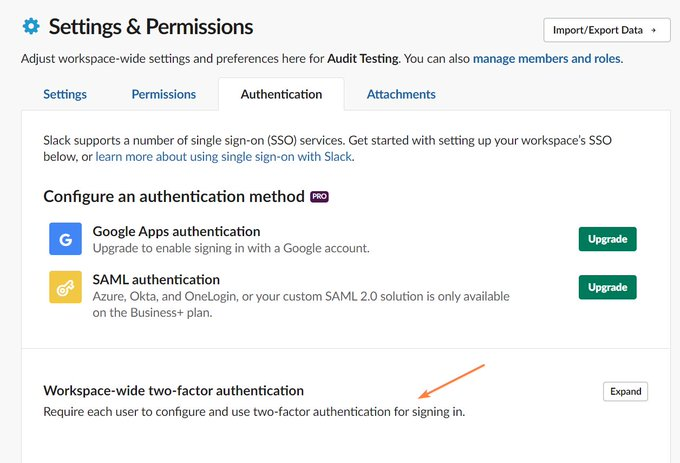
Set up policies with your team, Discord admins, and anyone in a position to approve any dangerous requests that ALL requests need to go through Slack. For extremely dangerous requests you could require more, i.e. Email, Slack + PGP signature. But set up the procedures now.
This also has the added benefit of keeping your team's internal communications private in the case that your Discord ever does get breached. I would say the vast majority of projects do not have all of the above set up currently, so please, set it up before it is too late.
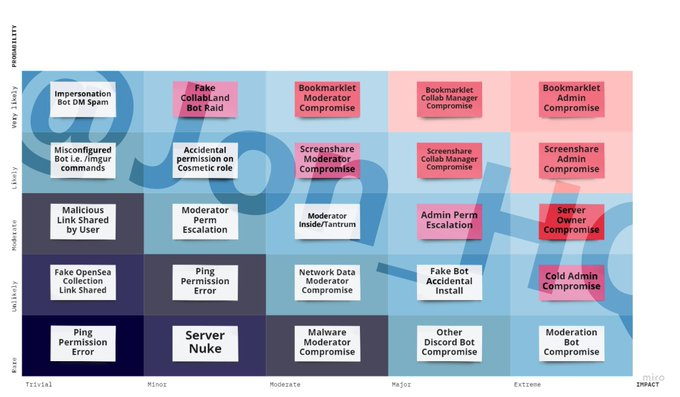
Risk Matrix of Potential Attacks
Discord Tip of the Day
The last couple of weeks has seen a drastic shift in types of attacks against Discords... I sat down and tried to create a risk matrix of both the severity and the impact of these different methods - let me know what you think!

Member discussion